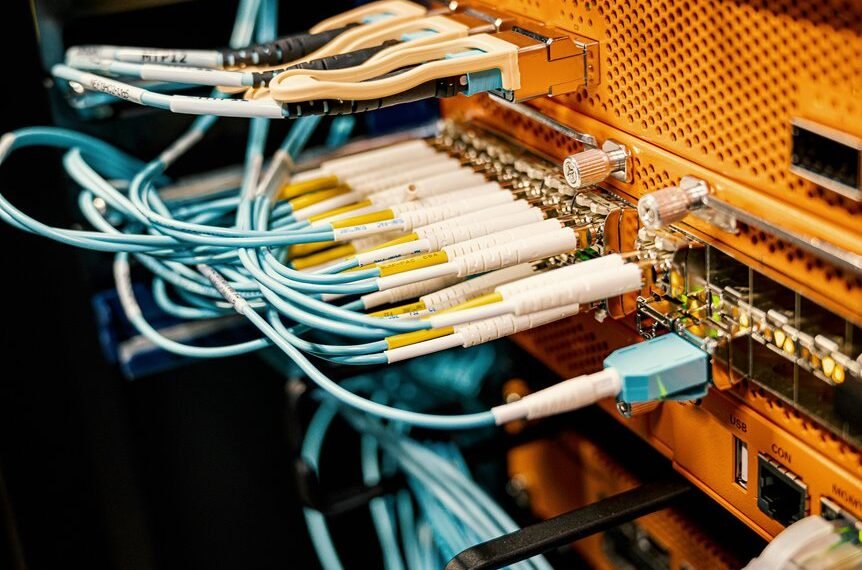
Advanced Cloud Hub 7177872104 employs a robust security framework designed to address modern cybersecurity challenges. Its implementation of advanced threat detection and real-time monitoring aids in identifying vulnerabilities before they can be exploited. Additionally, the use of encryption safeguards sensitive data during storage and transmission. Coupled with multi-factor authentication, these features create a formidable defense against unauthorized access. However, understanding how to effectively utilize these tools is essential for maximizing security.
Understanding the Security Features of Advanced Cloud Hub 7177872104
As organizations increasingly adopt cloud-based solutions, understanding the security features of Advanced Cloud Hub 7177872104 becomes essential for safeguarding sensitive data.
This platform emphasizes cloud compliance through robust policies and frameworks, ensuring adherence to regulations.
Additionally, its advanced threat detection capabilities utilize real-time monitoring and analytics to identify vulnerabilities, enabling organizations to proactively mitigate risks and maintain data integrity in a dynamic cloud environment.
How Does Encryption Protect Your Data in the Cloud?
Encryption serves as a fundamental mechanism for protecting data in cloud environments, complementing the security features of platforms like Advanced Cloud Hub 7177872104.
Multi-Factor Authentication: Adding an Extra Layer of Security
Security enhancement is a critical objective for organizations utilizing cloud services, and multi-factor authentication (MFA) emerges as a pivotal strategy in this endeavor.
Best Practices for Utilizing Advanced Cloud Hub Security Tools
How can organizations effectively leverage advanced cloud hub security tools to enhance their security posture?
By implementing robust cloud access controls, organizations can restrict unauthorized entry while optimizing user permissions.
Additionally, employing advanced threat detection mechanisms allows for real-time identification of vulnerabilities.
Regular audits and updates of security configurations further ensure that defenses remain effective against evolving threats, fostering a proactive security environment.
Conclusion
In summary, Advanced Cloud Hub 7177872104 exemplifies robust security through its comprehensive policies, advanced encryption techniques, and multi-factor authentication. For instance, consider a hypothetical financial institution that successfully thwarted a data breach attempt through real-time monitoring and analytics, safeguarding millions in sensitive customer information. Such scenarios highlight the critical importance of employing advanced security measures in cloud environments, ensuring data integrity and compliance while significantly reducing the risk of unauthorized access and potential data loss.