The security framework of Advanced Enterprise Platform 503032132 employs a structured approach to safeguarding sensitive information. It integrates access controls, encryption, and multi-factor authentication to mitigate risks. Continuous monitoring and real-time analytics play a crucial role in identifying vulnerabilities. This layered defense mechanism not only enhances data integrity but also builds user confidence. However, the effectiveness of these measures in the face of evolving cyber threats raises critical questions about future adaptability.
Understanding the Core Security Features of Platform 503032132
As organizations increasingly rely on Platform 503032132 for their enterprise needs, understanding its core security features becomes essential for safeguarding sensitive data.
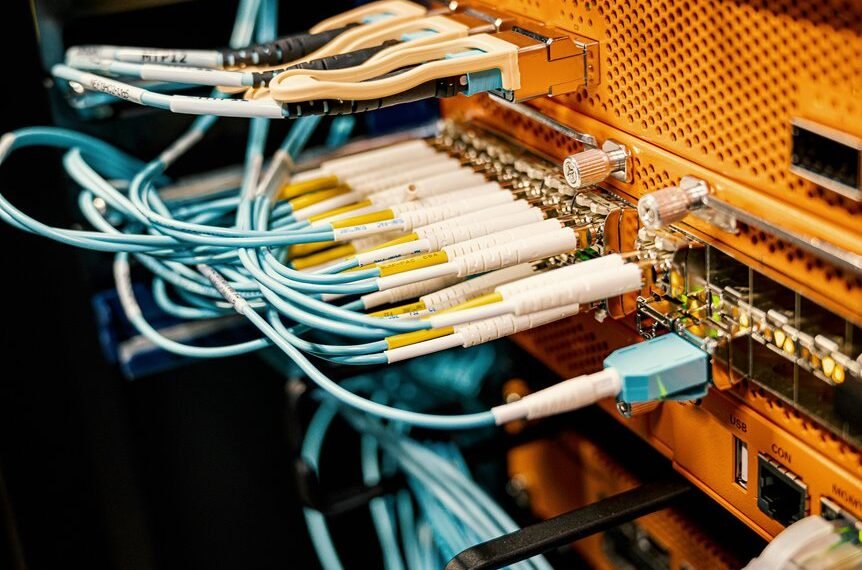
Key components include robust access controls, which limit user permissions and mitigate unauthorized access, and mechanisms ensuring data integrity, safeguarding against corruption or alteration.
These features collectively enhance security posture, allowing organizations to maintain control over their data while fostering operational freedom.
How Does Encryption Safeguard Your Data on Platform 503032132?
How can encryption effectively protect sensitive data on Platform 503032132?
By employing robust encryption methods, the platform ensures data protection through transformation of readable information into an encoded format. This process secures data against unauthorized access, maintaining confidentiality and integrity.
Furthermore, encryption facilitates compliance with regulatory standards, thereby enhancing user trust and safeguarding personal freedoms associated with data handling and storage.
Implementing Multi-Factor Authentication for Enhanced Protection
Encryption serves as a foundational element in safeguarding data on Platform 503032132, but the implementation of multi-factor authentication (MFA) significantly enhances overall security.
The Role of Continuous Monitoring in Threat Detection and Response
Continuous monitoring plays a crucial role in the proactive detection and response to potential threats within enterprise platforms.
By leveraging real-time analytics, organizations can effectively navigate the evolving threat landscape, identifying anomalies and vulnerabilities as they arise.
This dynamic approach not only enhances situational awareness but also facilitates timely interventions, empowering enterprises to mitigate risks and safeguard critical assets against sophisticated cyber threats.
Conclusion
In conclusion, Advanced Enterprise Platform 503032132 Security exemplifies a comprehensive approach to data protection through its integration of access controls, encryption, MFA, and continuous monitoring. Critics may argue that such multifaceted security can complicate user experience; however, the streamlined design and real-time analytics significantly enhance operational efficiency without sacrificing security. By investing in this dynamic framework, organizations not only fortify their defenses against evolving cyber threats but also cultivate a foundation of trust and resilience in their data management practices.