Advanced IT cloud security is crucial for organizations transitioning to cloud environments. It encompasses various strategies, including robust encryption and effective identity management. These measures protect sensitive information during transfer and storage. Continuous monitoring and real-time threat detection are also vital for identifying vulnerabilities. As security landscapes evolve, understanding current technologies and best practices becomes imperative for maintaining a strong defense. Future developments in this area may reshape security protocols significantly.
Understanding Advanced IT Cloud Security Solutions
As organizations increasingly migrate to cloud environments, understanding advanced IT cloud security solutions becomes imperative for safeguarding sensitive data.
Effective strategies incorporate cloud encryption to protect data at rest and in transit, ensuring confidentiality.
Additionally, robust threat detection mechanisms are essential for identifying and responding to potential vulnerabilities in real-time.
Together, these elements form a comprehensive approach to maintaining security and freedom in cloud operations.
Key Technologies Enhancing Cloud Security at 8442006330
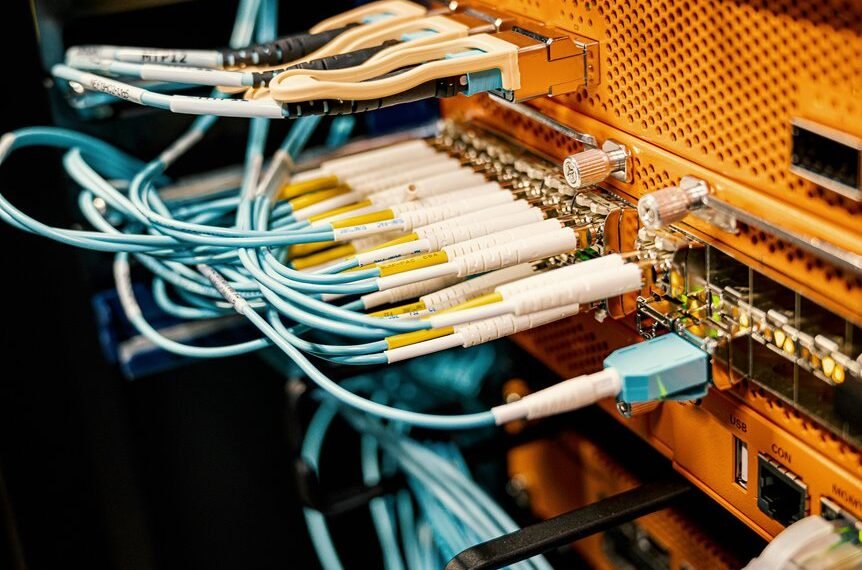
Advanced IT cloud security relies on a variety of key technologies that enhance the protection of data and applications in cloud environments.
Notably, robust encryption protocols safeguard sensitive information during transmission and storage, while effective identity management systems ensure that access is granted only to authorized users.
These technologies work in tandem to create a resilient security framework, promoting data integrity and user trust.
Best Practices for Implementing Cloud Security Measures
Although implementing cloud security measures can be complex, adhering to best practices is essential for ensuring robust protection of cloud environments.
Organizations should prioritize stringent access control policies to limit user permissions and reduce vulnerabilities. Additionally, employing data encryption techniques safeguards sensitive information, both in transit and at rest.
Regular audits and compliance checks further enhance security posture, fostering a resilient cloud infrastructure.
The Future of Cloud Security: Trends and Predictions
While the cloud security landscape continues to evolve rapidly, emerging technologies and shifting threat vectors are shaping its future.
Future predictions indicate a rise in AI-driven security solutions, enhanced encryption methods, and decentralized identity management.
Organizations prioritizing adaptive security frameworks will better combat sophisticated threats, ensuring resilience.
The integration of blockchain technology may also redefine trust in cloud security protocols, enhancing user autonomy.
Conclusion
In conclusion, advanced IT cloud security solutions are vital for organizations navigating the complexities of cloud environments. While some may argue that implementing these measures can be resource-intensive, the potential risks of data breaches far outweigh the initial investment. By leveraging cutting-edge technologies and adhering to best practices, businesses can not only protect sensitive information but also enhance their overall operational resilience. Staying informed on emerging trends will further bolster their defenses against evolving cyber threats.