Advanced IT Hub 963008707 Security employs a range of sophisticated technologies to protect sensitive data. Its use of advanced encryption and stringent access controls ensures data integrity both in transit and at rest. The organization also implements proactive strategies, such as threat intelligence and incident response planning. However, as cyber threats continue to evolve, the effectiveness of these measures must be continually assessed and adapted. What innovative approaches might redefine their security landscape?
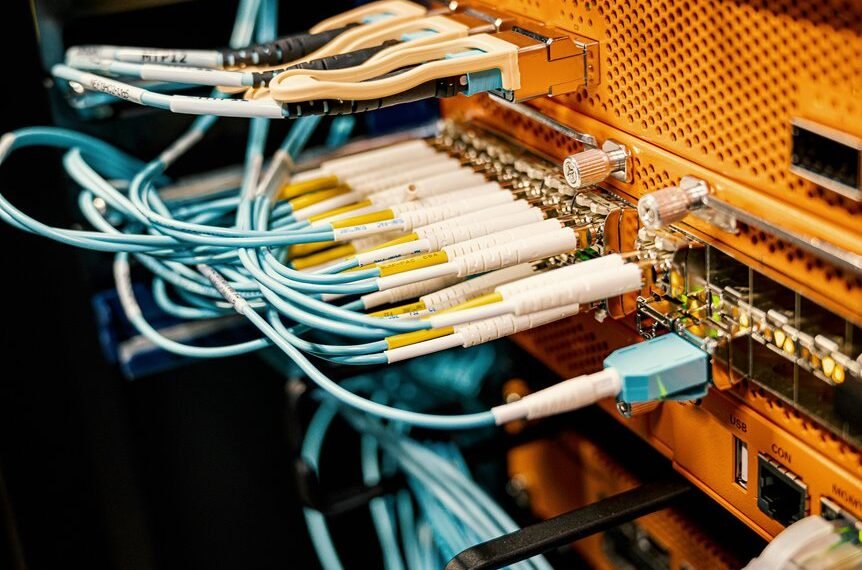
Key Security Technologies at Advanced IT Hub 963008707
In order to effectively safeguard sensitive data and maintain operational integrity, Advanced IT Hub 963008707 employs a comprehensive suite of security technologies.
These include advanced encryption methods that secure data in transit and at rest, alongside robust access controls that limit user permissions.
Proactive Strategies to Combat Cyber Threats
To enhance its defense mechanisms, Advanced IT Hub 963008707 adopts proactive strategies that directly address the evolving landscape of cyber threats.
By leveraging threat intelligence, the organization anticipates potential attacks and fortifies its security posture.
Additionally, a robust incident response plan ensures rapid containment and mitigation of breaches, empowering the hub to maintain operational integrity while safeguarding sensitive information from malicious actors.
Best Practices for Data Protection and Privacy
While organizations increasingly rely on digital infrastructures, implementing best practices for data protection and privacy becomes paramount to safeguard sensitive information.
Employing data encryption ensures that unauthorized access is mitigated, while adherence to privacy regulations establishes a framework for ethical data handling.
Regular audits and employee training further fortify defenses, promoting a culture of vigilance essential for maintaining trust and compliance in an evolving digital landscape.
The Future of Security at Advanced IT Hub 963008707
The future of security at Advanced IT Hub 963008707 promises to be shaped by an integration of innovative technologies and proactive strategies.
Anticipating security trends and addressing emerging threats will be crucial. This approach will involve leveraging artificial intelligence, machine learning, and advanced analytics to enhance threat detection and response capabilities, ensuring a robust security posture that aligns with the organization’s commitment to digital freedom.
Conclusion
In conclusion, Advanced IT Hub 963008707 exemplifies excellence in cybersecurity through its strategic synthesis of sophisticated technologies and proactive practices. By prioritizing protection, the organization not only fortifies data defenses but also fosters a forward-thinking framework for future security challenges. As the digital landscape evolves, the Hub’s commitment to continuous improvement and innovative integration ensures it remains a formidable force against emerging threats, effectively navigating the nexus of technology and trust in data protection.