Advanced IT Services 627970238 Security addresses the complexities of modern cybersecurity threats through its innovative solutions. By employing advanced threat detection and machine learning technologies, it enables organizations to identify vulnerabilities in real time. This tailored approach enhances risk management and operational continuity. However, the effectiveness of such services depends on various factors. Understanding these nuances can significantly influence an organization’s security strategy. What are the critical elements to consider when selecting the right partner?
Understanding Cybersecurity Threats in Today’s Landscape
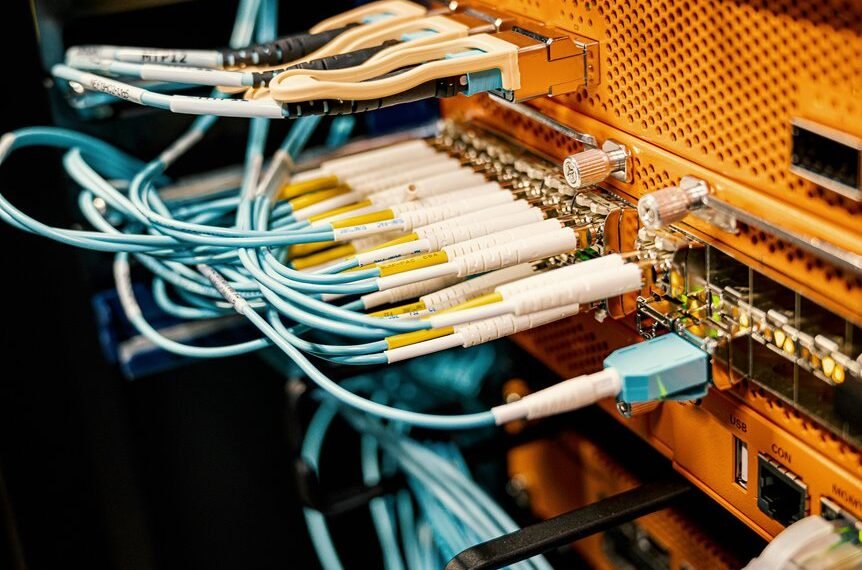
As organizations increasingly rely on digital infrastructure, understanding cybersecurity threats has become paramount for maintaining operational integrity.
Phishing attacks exploit human vulnerabilities, tricking users into revealing sensitive information. Meanwhile, ransomware threats pose a significant risk by encrypting critical data and demanding payment for its release.
Awareness of these evolving tactics is essential for organizations striving to safeguard their assets and ensure operational continuity in a digital landscape.
Key Features of Advanced IT Services 627970238 Security Solutions
The evolving landscape of cybersecurity threats necessitates robust security solutions that can adapt to emerging challenges.
Key features of Advanced IT Services 627970238 include sophisticated threat detection mechanisms, which utilize machine learning for real-time identification of anomalies.
Additionally, comprehensive risk assessment tools enable organizations to evaluate vulnerabilities effectively, ensuring that security measures are proactive and aligned with an organization’s unique risk profile and operational needs.
Benefits of Implementing Proactive Security Measures
Implementing proactive security measures significantly enhances an organization’s ability to safeguard its assets against evolving cyber threats.
These measures facilitate risk mitigation by identifying vulnerabilities and addressing them before exploitation occurs.
Furthermore, effective threat detection systems enable prompt responses to potential breaches, thereby minimizing damage.
Ultimately, such strategies empower organizations to maintain autonomy and resilience in an increasingly complex digital landscape.
How to Choose the Right IT Security Service for Your Business?
How can businesses effectively navigate the myriad of IT security services available in today’s market?
A thorough risk assessment is essential, identifying vulnerabilities and specific security needs.
Subsequently, conducting a vendor evaluation helps in comparing service offerings, expertise, and reputation.
Prioritizing providers that align with the organization’s values can empower businesses to choose solutions that enhance security while ensuring operational freedom and flexibility.
Conclusion
In conclusion, Advanced IT Services 627970238 Security stands as a vigilant guardian in the tumultuous sea of cybersecurity threats, akin to a lighthouse guiding ships away from perilous rocks. By leveraging advanced threat detection and tailored risk assessment tools, organizations can navigate the complexities of the digital landscape with confidence. With proactive security measures in place, businesses not only protect their critical assets but also ensure operational continuity, fostering resilience in an ever-evolving threat environment.