The security framework of Innovative Tech Hub 919268189 exemplifies a methodical approach to safeguarding both physical and digital assets. By integrating biometric authentication and advanced cybersecurity measures, the hub ensures that access and information remain tightly controlled. In addition, physical security elements, such as surveillance systems, complement these efforts. However, the effectiveness of these strategies hinges on a well-coordinated emergency response plan. Analyzing each component reveals critical insights into the overall security landscape.
Innovative Access Control Measures at 919268189
Innovative access control measures at 919268189 exemplify a progressive approach to securing digital and physical environments.
The integration of biometric authentication ensures that only authorized personnel gain access, enhancing security through unique biological identifiers.
Furthermore, keyless entry systems streamline access while reducing reliance on traditional keys, promoting user convenience.
These methods collectively foster a secure, efficient environment that prioritizes individual freedom and security.
Cybersecurity Protocols to Protect Sensitive Data
A comprehensive set of cybersecurity protocols is essential for safeguarding sensitive data in today’s digital landscape.
Employing robust data encryption techniques ensures that information remains secure during transmission and storage.
Additionally, implementing advanced threat detection systems allows organizations to identify and mitigate potential breaches proactively.
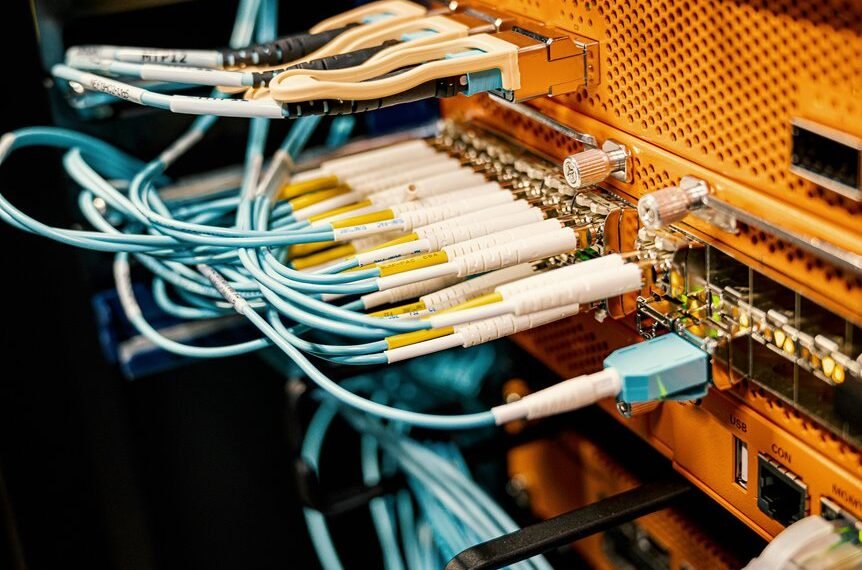
Physical Security Features for a Safe Environment
While digital security measures are vital, the importance of physical security features cannot be overlooked in creating a safe environment for organizations.
Effective surveillance systems enhance monitoring capabilities, deterring unauthorized access. Additionally, perimeter fencing establishes a robust boundary, significantly reducing vulnerability to external threats.
Together, these elements form a foundational layer of security that complements digital protocols, ensuring comprehensive protection for the tech hub.
Emergency Response Strategies for Tech Hub Security
Although unexpected incidents can disrupt operations at a tech hub, having well-defined emergency response strategies is essential for minimizing risks and ensuring swift recovery.
Effective crisis management involves comprehensive evacuation plans, tailored communication protocols, and regular drills.
Conclusion
In conclusion, Innovative Tech Hub 919268189 exemplifies a fortress of innovation, where security measures resemble the intricate layers of an onion—each layer meticulously crafted to shield against potential threats. Just as an onion’s protective layers must be peeled away to reach its core, the hub’s comprehensive security infrastructure ensures that only authorized individuals access its valuable resources. This commitment to safety not only fosters a thriving environment for technological advancement but also instills confidence among stakeholders in an increasingly complex digital landscape.