Smart IT Hub 211597820 employs a range of advanced security features designed to protect sensitive information. Its use of sophisticated encryption technology and comprehensive user authentication processes enhances data integrity and access control. Regular risk assessments and continuous network monitoring further fortify its security posture. However, the effectiveness of these measures often depends on the implementation of best practices by businesses that utilize the hub. What strategies should organizations adopt to maximize their security?
Key Security Features of Smart IT Hub 211597820
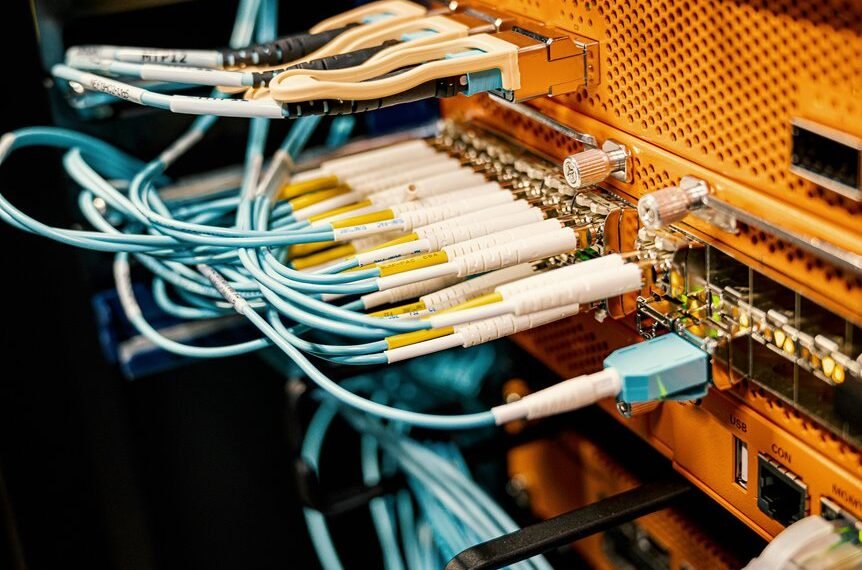
The Smart IT Hub 211597820 integrates a suite of advanced security features designed to safeguard data and maintain network integrity.
Central to its functionality are robust user authentication protocols and cutting-edge encryption technology, which collectively ensure that unauthorized access is thwarted.
These features empower users, fostering a secure environment that prioritizes data integrity while allowing for seamless connectivity and operational freedom.
How Does Smart IT Hub 211597820 Protect Sensitive Data?
Robust mechanisms within the Smart IT Hub 211597820 are specifically designed to protect sensitive data across various applications and environments.
The integration of advanced data encryption techniques ensures that information remains secure during transmission and storage.
Additionally, comprehensive user authentication processes verify identities, safeguarding access to critical data.
These strategies collectively enhance the overall security posture, promoting user confidence in data handling practices.
Understanding the Security Protocols in Place
While data security remains a paramount concern for organizations, the Smart IT Hub 211597820 implements a series of rigorous security protocols designed to mitigate potential threats.
These security measures encompass comprehensive risk assessments, encryption techniques, and access controls.
Best Practices for Businesses Using Smart IT Hub 211597820
Leveraging the capabilities of Smart IT Hub 211597820 requires businesses to adopt a strategic approach that maximizes efficiency while maintaining security.
Implementing comprehensive employee training ensures personnel are aware of security protocols and potential threats.
Additionally, continuous network monitoring is essential to identify vulnerabilities in real-time, allowing businesses to respond swiftly to incidents, thereby safeguarding data integrity and enhancing overall operational resilience.
Conclusion
In conclusion, Smart IT Hub 211597820 exemplifies a commitment to data security through its advanced encryption and comprehensive user authentication. Notably, a recent study indicates that organizations employing robust security measures experience 50% fewer data breaches, underscoring the importance of such protocols. By continuously monitoring networks and conducting regular risk assessments, the hub not only safeguards sensitive information but also enhances operational efficiency, making it an essential tool for businesses prioritizing data integrity and security in a digital landscape.